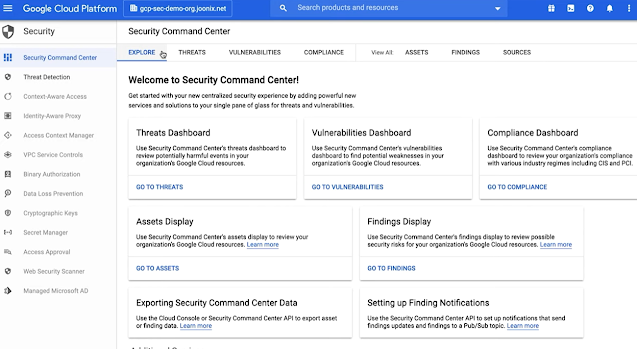
GCP SCC
-------------
Security Command Center is Google Cloud's centralized vulnerability and threat reporting service. Security Command Center helps you strengthen your security posture by evaluating your security and data attack surface; providing asset inventory and discovery; identifying misconfigurations, vulnerabilities and threats; and helping you mitigate and remediate risks
To use Security Command Center, you must have an Identity and Access Management (IAM) role that includes appropriate permissions:
- Security Center Admin Viewer lets you view Security Command Center.
- Security Center Admin Editor lets you view Security Command Center and make changes.
The Threats dashboard helps you review potentially harmful events in your organization's Google Cloud resources.
- Threats by severity shows the number of threats in each severity level.
- Threats by category shows the number of findings in each category across all projects.
- Threats by resource shows the number of findings for each resource in your organization.
The threats dashboard displays results for the time period you specify in the drop-down list. The drop-down list has several options between 1 hour and "all time," which shows all findings since the service was activated. The time period you select is saved between sessions.
No comments:
Post a Comment